In large-scale security and communications projects, compliance often defines procurement, but it does not guarantee performance. The gap between specification and execution is where systems succeed or fail under real operating conditions. By: Abed Tabbara,Executive Vice President, Hader
Building Management Systems across the EMEA region are moving beyond automation and evolving into integrated platforms shaped by data-driven intelligence. This shift comes as the very idea of the “intelligent” building is being redefined by stricter environmental regulation, growing cybersecurity demands, and rising user expectations. By: Mirza Bahic E-mail:
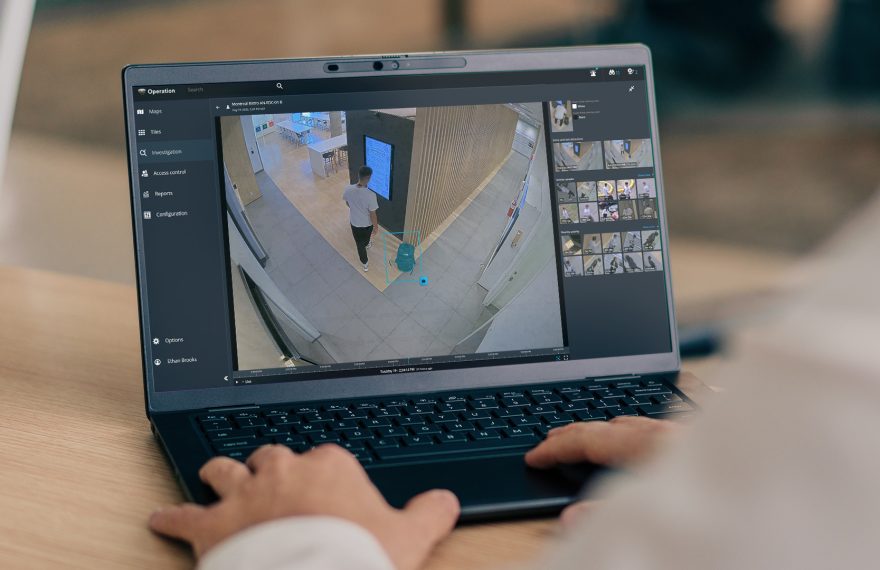
Intelligent search reflects a practical evolution in how video is used during investigations. Rather than changing what security teams do, it changes how quickly and confidently they can do it. By simplifying review workflows and reducing manual effort, intelligent search helps teams manage investigation workloads more effectively. By: Hassan Makki, Area Sales
Mobile credentials are slowly becoming the new standard in access control. Their growing adoption is shaped by security rather than convenience, reducing long-term operational costs, and the need to support hybrid environments where mobile and physical credentials coexist By: Sam Cherif, Senior Director, Middle East & Africa, ASSA ABLOY Opening Solutions E-mail:
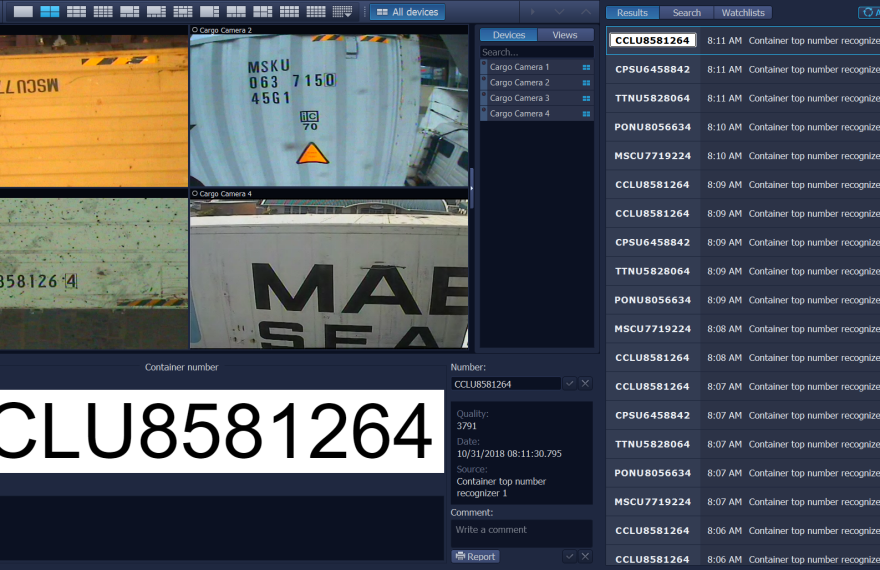
Seaports across the GCC are deploying the SecurOS® Video Intelligence Platform to unify cargo, vehicle, and security operations, enabling high-throughput logistics and real-time oversight within a single AI-driven environment. By: Sandy Issa, Marketing Manager, Middle East, Intelligent Security Systems E-mail: sandy.issa@issivs.com Major commercial seaports across the
When it comes to security in data centers, cyberattacks very much dominate the headlines. But among the multiple heightening challenges caused by the AI-driven proliferation of facilities is the threat of physical security failures. Peter Dempsey from Axis explains how data center growth is transforming security needs By: Editorial, a&s Middle East E-mail:
iXAfrica built a highly resilient, carrier-neutral data center in Nairobi to support East Africa’s digital transformation. By implementing an integrated security approach, the company achieved full visibility, stronger compliance, and a scalable foundation for protecting critical infrastructure as it grows By: Sienna Cacan, Enterprise Segment Marketing Manager, Axis
Across the Middle East, cargo security is undergoing a structural transformation. Trade volumes continue to grow as new ports, logistics corridors, and border infrastructures expand under national development strategies. At the same time, the nature of security risks has evolved. Modern threats are smaller, more modular, and increasingly designed to exploit the limitations
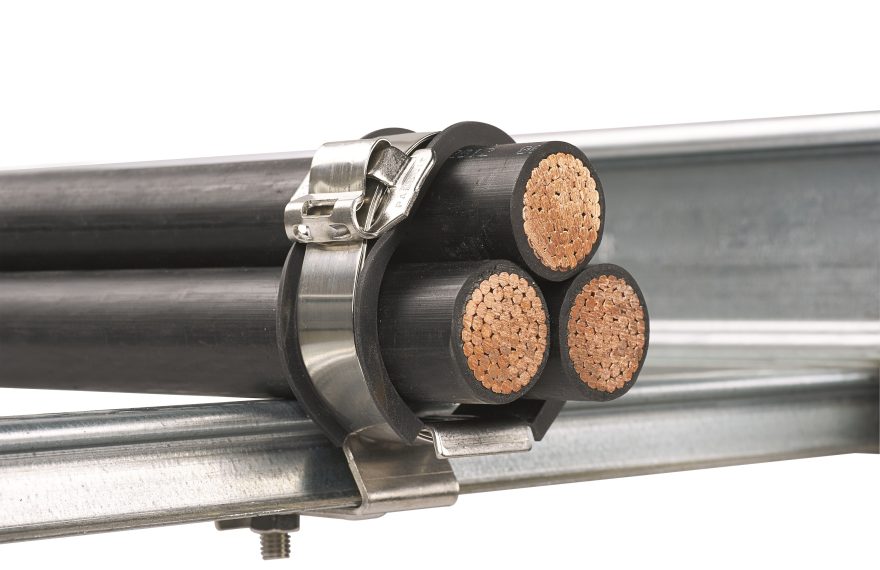
As data center workloads and power demands grow, short circuits can generate extreme forces within milliseconds. Panduit’s cable restraint solutions, developed and tested according to IEC 61914:2021, help protect infrastructure, personnel and operational continuity By: Martin Kandziora, Senior Manager Marketing EMEA, Panduit GmbH E-mail: Martin.Kandziora@panduit.com On the
By eliminating cables, extending battery life, maximizing coverage, and leveraging AI to reduce inefficiencies, Reconeyez offers a low total cost of ownership that aligns perfectly with the demands of the Middle East market—where protecting vast, high-value assets must be both effective and economically sustainable By: Andy Keeley, Marketing Director, Reconeye E-mail: