Sophos Survey Finds Trust Gap Is Reshaping Cybersecurity Decisions
A new Sophos report suggests trust has become one of the cybersecurity sector’s biggest weak points in 2026, with most IT leaders struggling to assess vendors and many linking low confidence to higher operational risk and greater pressure to change providers
Trust is becoming a defining issue in cybersecurity purchasing and operations, according to new research published by Sophos. The company said its latest findings are based on an independent global survey of 5,000 IT and security decision-makers across 17 countries, conducted by Vanson Bourne to examine how organizations evaluate cybersecurity vendors.
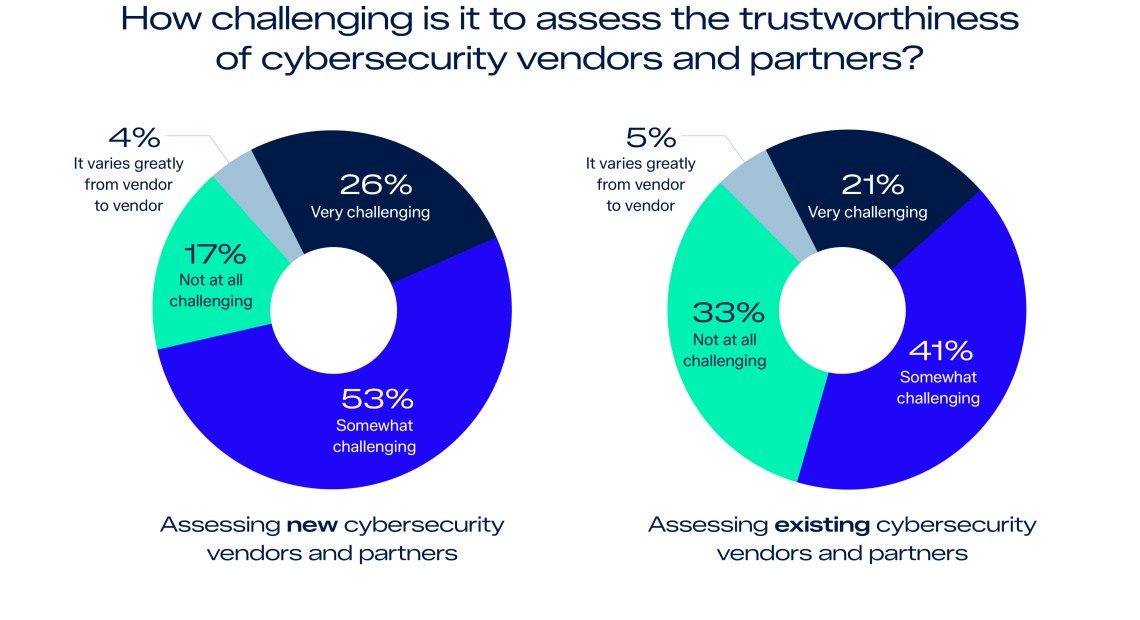
As reported by Sophos, only 5% of IT leaders said both they and their organizations have full trust in their cybersecurity vendors. The study also found that 79% of respondents consider it difficult to assess the trustworthiness of new cybersecurity providers, while 62% said the same challenge applies even to vendors they already work with.
Sophos said verified evidence of cybersecurity maturity is now one of the strongest drivers of trust, reflecting growing pressure on vendors to back up claims with clearer proof and greater transparency. The report also found that 47% of respondents felt vendor information was not factual or detailed enough, while 45% said the information they receive is difficult to interpret.
The operational impact of this trust gap appears significant. According to Sophos, 51% of respondents said limited trust increases concern that their organization could suffer a major cyber incident, while 45% said it makes them more likely to switch vendors. Another 42% linked weak trust to higher oversight requirements.
For the wider security market, the findings matter because they reinforce how cybersecurity decisions are no longer based only on product performance, but also on transparency, governance, and confidence in vendor claims. That is particularly relevant as cyber and physical security environments become more connected through cloud platforms, video systems, identity tools, and critical infrastructure applications. This final point is an industry inference based on the report’s findings rather than a direct Sophos claim.
Graph courtesy of SOPHOS